Public version, available here.
By Tom Clare
Netskope continues to advance inline threat protection capabilities and has improved its detection and blocking of malware and phishing attacks while also lowering and improving its false positive rate in the latest AV-TEST Report. In every part of the testing, Netskope improved.
Today more than half of user egress traffic involves applications and cloud services rather than websites, and where more than half of threats are delivered knowing these popular domains are allowed, or worse yet bypassed from inline threat inspection altogether. Relying on endpoint protection for executable malware leaves a blind spot for fileless attacks using fake login forms and phishing techniques hosted in applications and cloud services that require inline content and context inspection to protect users. This dynamic changes the playing field for threat protection testing and what must be prioritized with respect to detection speed and efficacy scores.
First, user experience is number one today with high performance access to SaaS applications, cloud services, and websites from any location and device. This provides a single pass TLS inspection cloud service about 10ms to decode and detect unknown zero-day threats in real-time for egress traffic. The innovations of generative AI and machine learning add a new set of detection engines inline for real-time detection with the key requirement of providing the content to these new defenses. If you bypass inspection of popular office suites or rely on legacy defenses unable to decode and inspect inline applications and cloud services, the attackers are ahead of you. If the content is not inspected inline, new AI/ML-based defenses cannot help you for inline real-time threat or data protection.
Attacks are shorter lived today, changing behavior frequently to avoid detection and often targeting specific users. The decades old defense concept of herd immunity, of being part of a large herd where one member gets infected so the herd can learn about the infection (i.e., patient zero) and then provide signature updates to protect others, assuming you have time on your side. To keep the gate closed on known threats, the herd mentality still works. However, for new unknown and zero-day threats you need to focus on threat efficacy in real-time at time-zero (T+0) for the breadth of executable (PE files), non-executable (non-PE files), and phishing attacks.
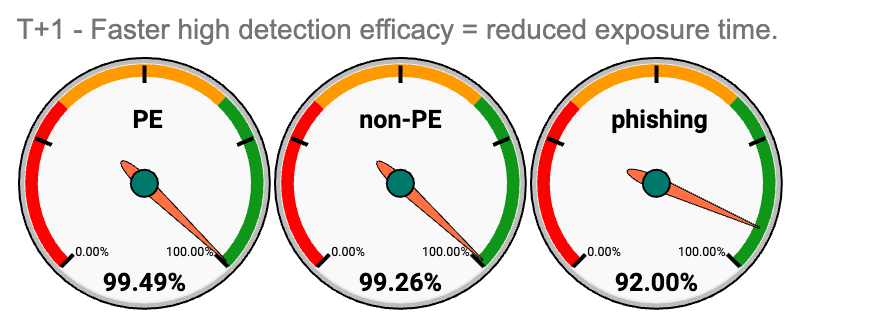
To show how quickly a threat protection defense can learn about unknown threats from T+0, AV-TEST also analyzed T+1-hour detection rates. Once you expand to T+4 hours or longer the herd effect factors into the efficacy results with threat intel updates. Threat efficacy reports must clearly call out T+0, T+1, and T+4 results so you can understand real-time threat efficacy and protection, and how fast the protection learns about new attacks. Simply put, you want the best T+0 real-time detection rating with the lowest false positive rating, backed by the best T+1 detection rating to quickly learn and block new attacks.
Once you get to T+4 detection ratings or longer, vendor herd immunity comes into effect and efficacy should be roughly on par unless the vendor has a very poorly-designed solution and/or they are not investing in valuable threat intel feeds. Single detection results in threat efficacy test reports are often unlabeled T+4 results or longer, showing the highest percentages possible due to herd threat intel sharing and masking the T+0 reality for real-time detection of the solution. Ask for the chart below when analyzing and comparing threat efficacy rates.
Digging deeper into the details, it’s important to realize that an inline defense must quickly inspect content for unknown and zero-day threats and does not have the luxury of time like endpoint protection solutions that monitor the file system, directory, and process tree. The inline defense does have an advantage in its ability to decode and inspect application and cloud service content, which pairs well with AI/ML defenses that require content an endpoint cannot always provide. A similar advantage emerges versus legacy sandboxing focused on executables in a virtual OS that is unlikely to decode content for apps and cloud services. For example, AI/ML defenses can detect encrypted files, compromised access and devices, phishing pages, and fake forms, plus many other content and context related variables of a threat. Attacks work in kill chains where detecting earlier stages is preferred when possible. For example, ransomware kill chain stages may include compromised remote access or phishing to then enable malware delivery. Detecting phishing attacks in real-time can stop the ransomware kill chain before data encryption, exfiltration, and malware delivery.
To put the concepts above to the test, Netskope recently completed a set of anti-malware tests with AV-TEST, an independent anti-malware testing lab based in Germany that owns one of the world’s largest databases of malware samples. Every second, AV-TEST discovers four to five new malware variants. This sums up to around 10 million new malware every month, and more than one billion malware objects in total in AV-TEST’s database.
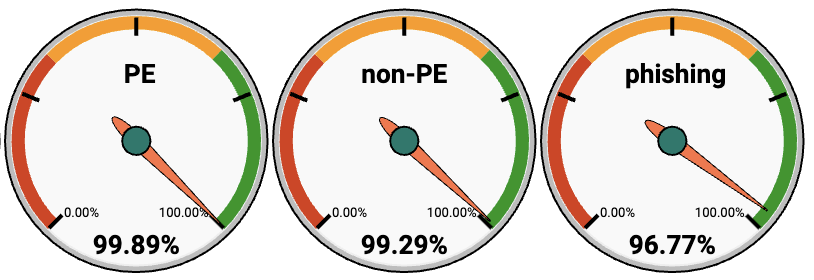
In November 2023, AV-TEST performed a test of the Netskope Intelligent Security Service Edge (SSE) threat protection offering, focusing on blocking efficacy vs malicious URLs with and without portable executable (PE) files and phishing websites, all while measuring false positive rates. The test evaluates protection at ‘time zero’ (T+0) as well as one hour later (T+1) and four hours later (T+4). The full test report can be viewed here.
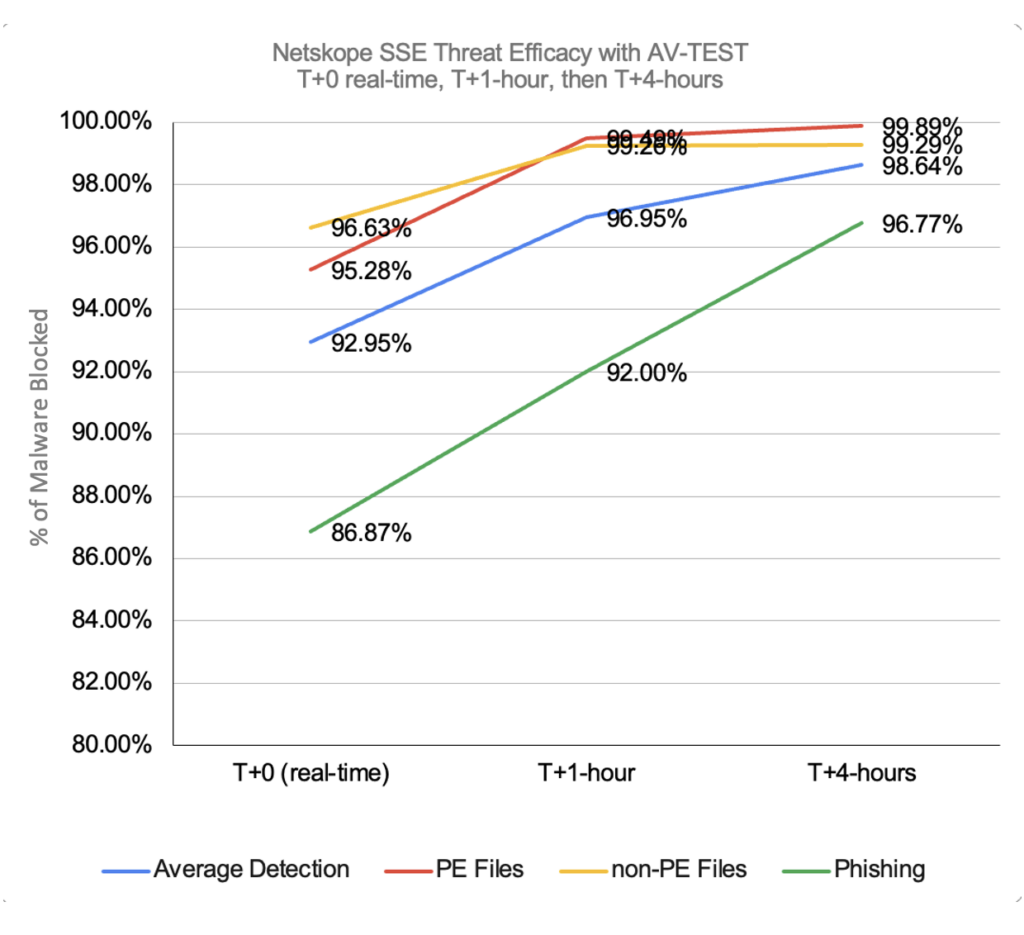
Netskope improved all of its threat efficacy ratings across T+0, T+1-hour, and T+4-hours since the prior AV-TEST in May 2022, and lowered false positive ratings to 0.58% at T+0. The chart above shows how real-time detection is ground zero for unknown and zero-day threat protection, then the increasing slope of the lines to learn new attacks within an hour, plus the four-hour perspective of sharing threat intel between multiple herds. Threat intel updates several times per hour keep the Netskope community protected with the advantage of AI/ML-based defenses inline for real-time protection of malicious PE files and phishing attacks. If you are four hours late to click on a threat link the odds are you are well protected, but if you are targeted to be the first or only user to click, then T+0 results become critical.
Netskope Intelligent SSE threat protection was configured with standard and advanced threat defense licenses. Security risk categories were blocked, however, uncategorized websites and potentially risky sites were allowed. Netskope Cloud Firewall was licensed and active in the testing to allow egress web traffic on ports 80/443 for TLS inspection and to block non-web traffic. Remote browser isolation (RBI), patient zero sandboxing to hold files until analyzed as clean, Cloud Threat Exchange for indicator of compromise (IOC) sharing, and user and entity behavior analytics (UEBA) detections and policies were all inactive for the testing.
Netskope has been rapidly improving threat protection defenses by providing inline machine-learning (ML) based detection of PE files to protect patient zero users from new malware and generative AI-based phishing detection in real-time. Sandboxing is also provided in both standard and advanced threat protection, plus Netskope continues to mature ML-based detection for malicious Office and PDF documents and offers multi-stage sandboxing for more than 30 file types with MITRE ATT&CK sandbox reporting. A sandbox API for file submissions, a RetroHunt API by file hash, and patient zero alerts on newly detected malware are also included.
Customers can further enhance threat protection with Netskope Remote Browser Isolation (RBI) of risky and uncategorized websites where no code executes on endpoints and Netskope Cloud Firewall with egress policy controls across ports and protocols by user, group, and OU with exceptions for FQDNs and wildcards. Behavior anomalies (UEBA) for high-risk users with ratings (User Confidence Index or UCI) and application destination ratings (low Cloud Confidence Index or CCI) can also be leveraged in adaptive access policies for enhanced patient zero protection. UCI has been instrumental in detecting insiders, compromise, and data exfiltration while CCI covers over 50,000 app and cloud service risk ratings.
Netskope Cloud Threat Exchange (CTE) is open to customers with no charge and automates bidirectional IOC sharing among customer security defenses. CTE makes near real-time checks for new IOCs from multiple sources and shares the threat intelligence with multiple solutions. The Intelligent SSE gateway inspects web and cloud user traffic in real-time, using defenses designed to inspect in less than 10ms for a performant user experience while CTE enables customers to manage timely IOC updates between defenses and threat intel sources.
Like your credit score or blood pressure, it takes a continuous and committed effort to improve and maintain healthy threat efficacy scores. Netskope provides a malware catch-rate service level agreement (SLA) next to its industry leading latency SLA of 10ms for unencrypted traffic, 50ms for encrypted traffic inspection, and 99.999% uptime for Netskope services on NewEdge, the world’s largest and highest performing security cloud. Learn more by requesting a demo or to run a real-time breach and attack simulation.







