This article will cover how to configure Single-Sign-On (SSO) for the Netskope Cloud Exchange (CE) platform using Okta. This will allow you to manage administrator access to CE from purely within Okta, rather than configuring administrators on the platform manually.
Cloud Exchange is different from the standard Netskope tenant you would have access to as a customer, and facilitates the exchange of information between your various security and operations platforms. For information on what Cloud Exchange is (including how to deploy it), please see here.
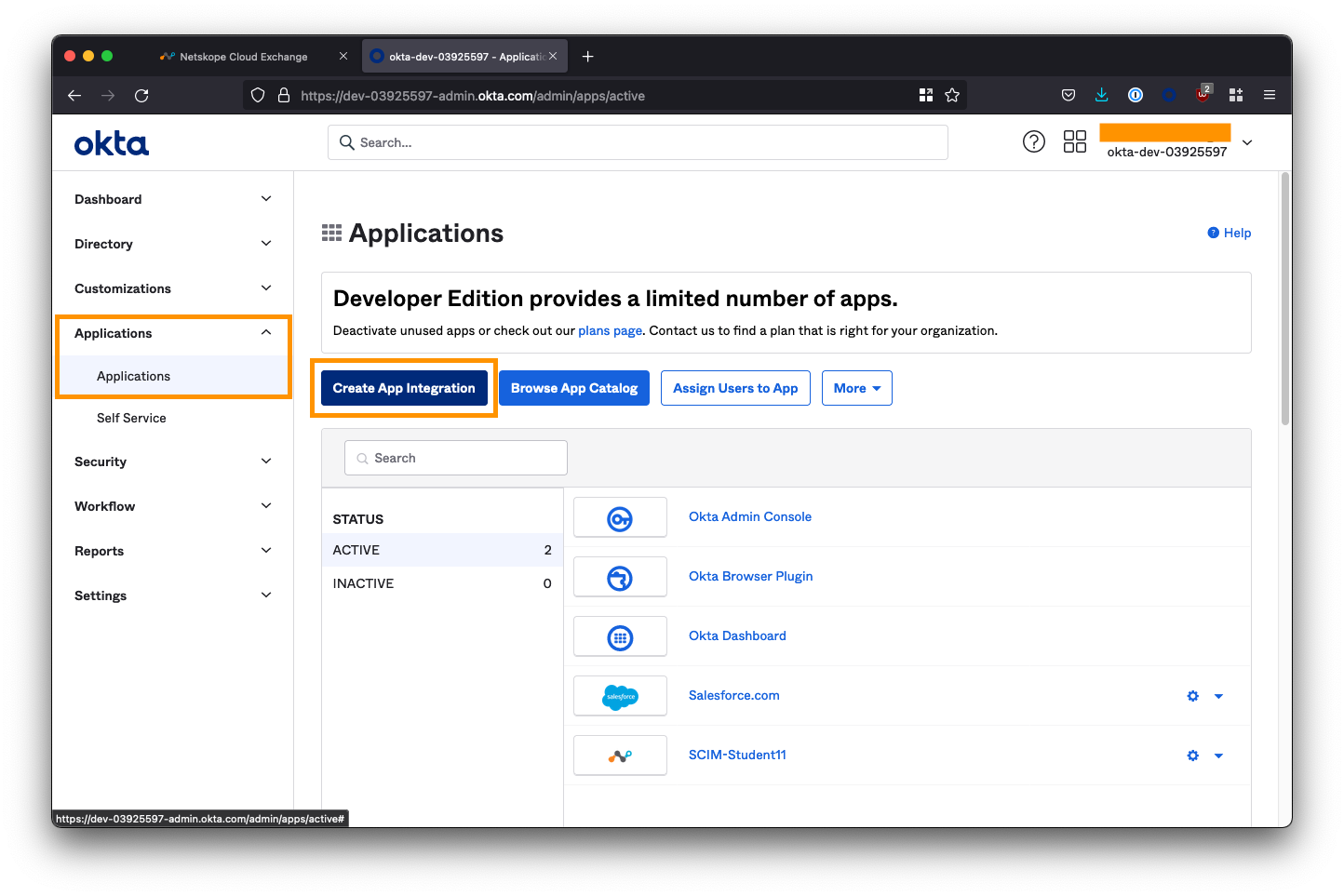
Create a new App Integration
Log in to your Okta administrator console and from the left-side menubar, navigate to Applications > Applications.
Select Create App Integration.
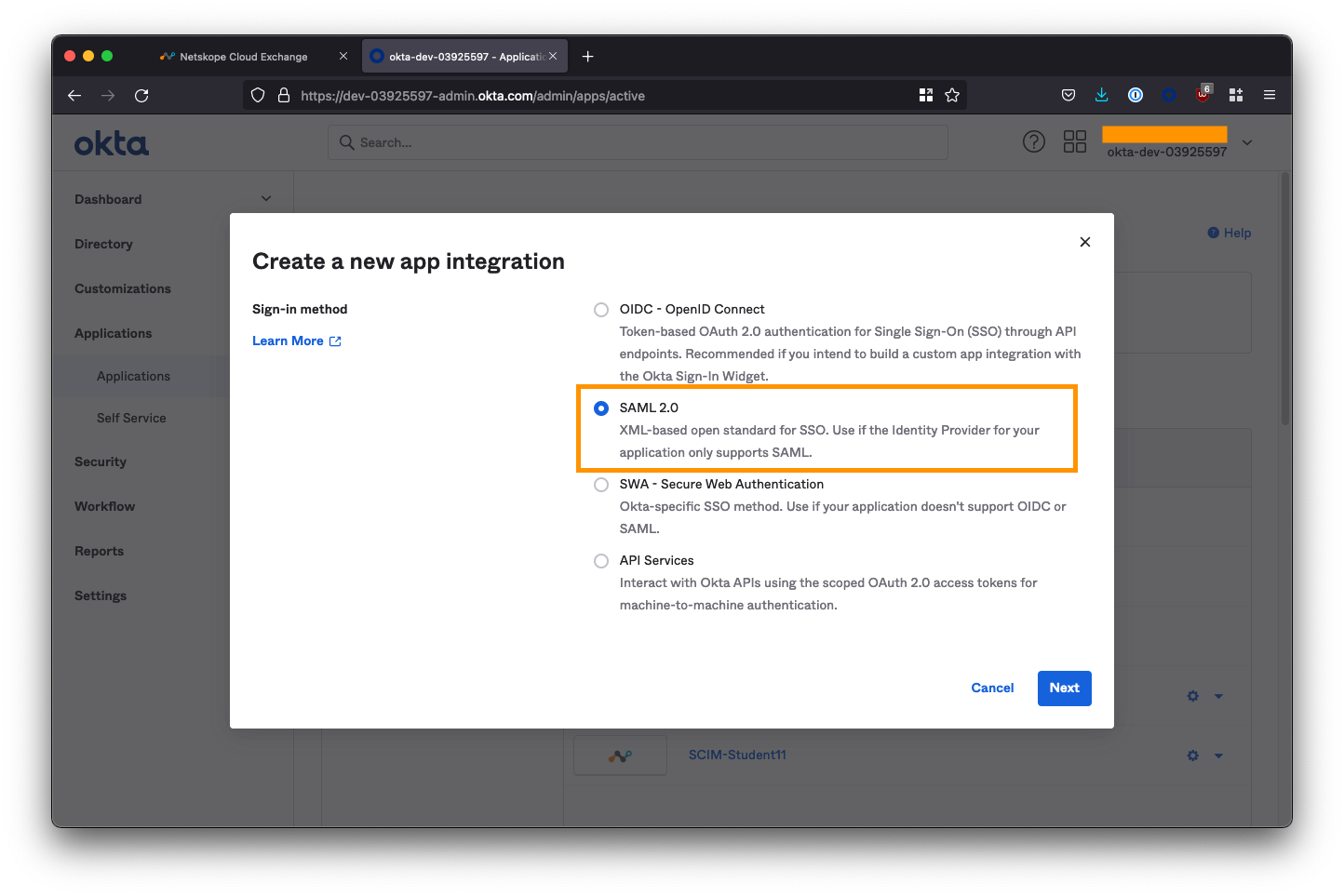
Select SAML 2.0 as the sign-in method and click Next.
On the next screen, set the App name to be Netskope Cloud Exchange and provide an app logo if required.
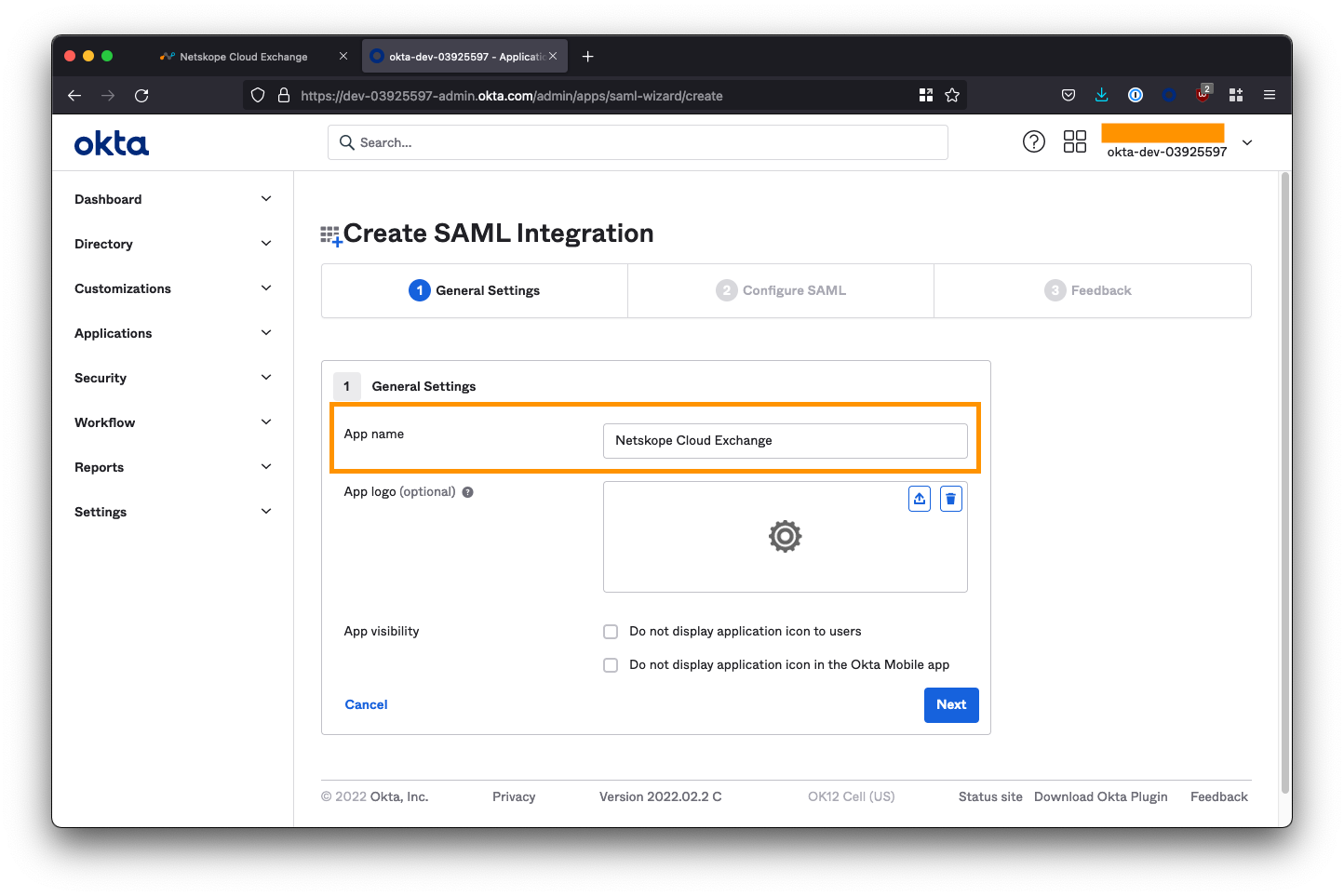
Click Next to proceed to the Configure SAML section.
Copy the Cloud Exchange SSO information
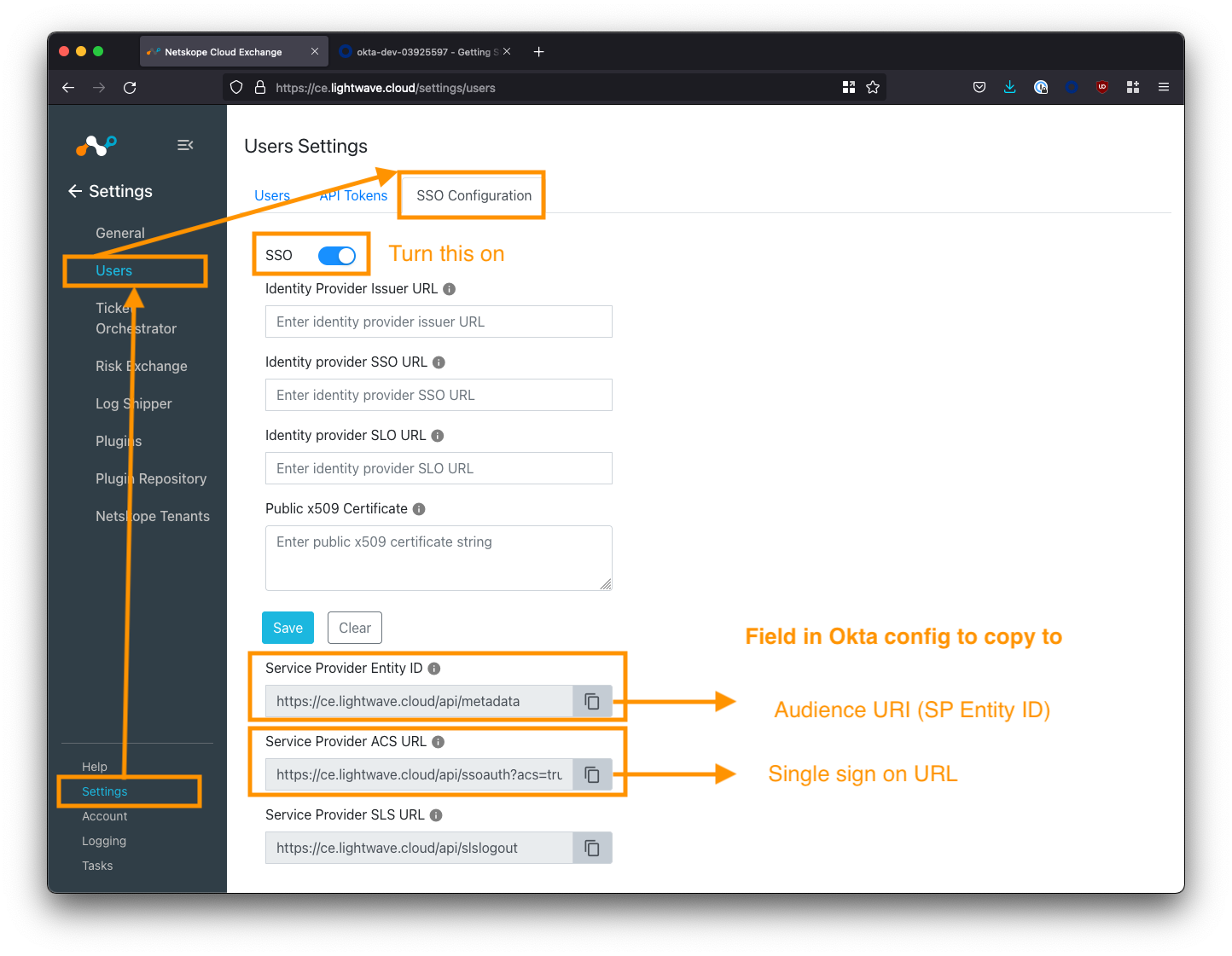
Log in to Cloud Exchange using the admin (super administrator) user, and navigate to Settings > Users (this settings area will only be visible to the admin user).
Select the SSO Configuration tab, and toggle the SSO toggle ON (make sure you save this configuration).
Note down the first two “Service Provider” fields at the bottom of the screen (Service Provider Entity ID and Service Provider ACS URL). The image below maps which URL should be used for which config field in Okta.
Configure Okta SAML Integration
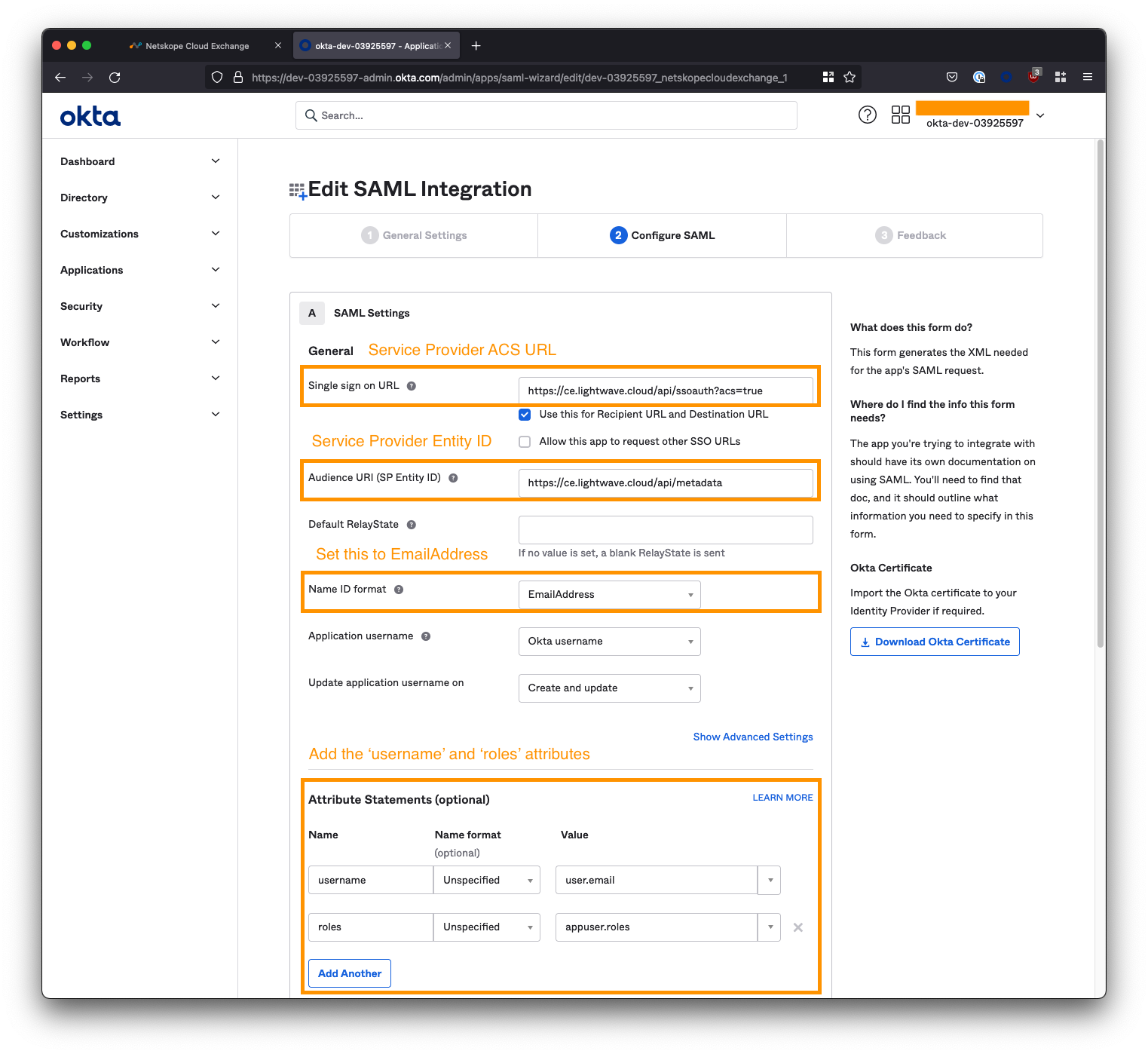
Switch back to your Okta configuration and configure the settings as follows:
Copy the Cloud Exchange Service Provider URLs
For the first two Service Provider URL fields in the Cloud Exchange SSO configuration, paste the corresponding URL into the appropriate field in Okta. See the table below for mapping:
| Cloud Exchange Field | Okta SAML Config Field |
|---|---|
| Service Provider Entity ID | Audience URL (SP Entity ID) |
| Service Provider ACS URL | Single sign on URL |
| Service Provider SLS URL |
N/A - Not used |
Set the Name ID format
Ensure you change the Name ID format in Okta, from Unspecified to EmailAddress.
Add additional attributes
You need to add two additional attribute statements to the Okta configuration: One called username and another called roles.
- The
usernameattribute should have the value ofuser.email. - The
rolesattribute should have the value ofappuser.roles(you will need to type this - it won’t appear in the dropdown).
Finish the SAML configuration
When you are done, scroll to the bottom of the page and click Next.
Check the box “I’m an Okta customer adding an internal app” and click Finish.
Open the Okta SAML 2.0 Steup Instructions
On the next page, click the View Setup Instructions button inside the yellow box under the Sign On tab app.
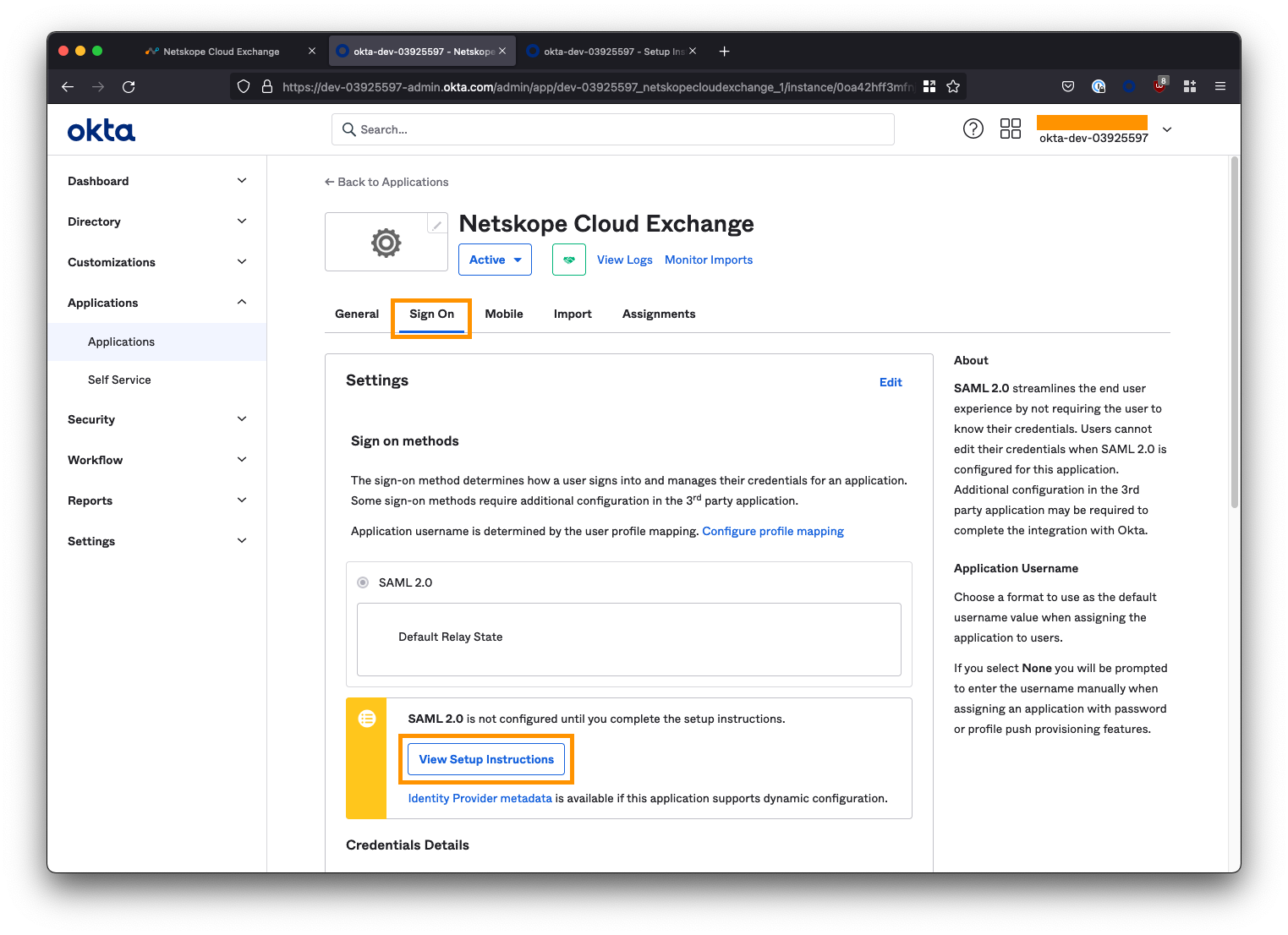
This will open a new tab containing the details we will need to copy back into the Cloud Exchange console.
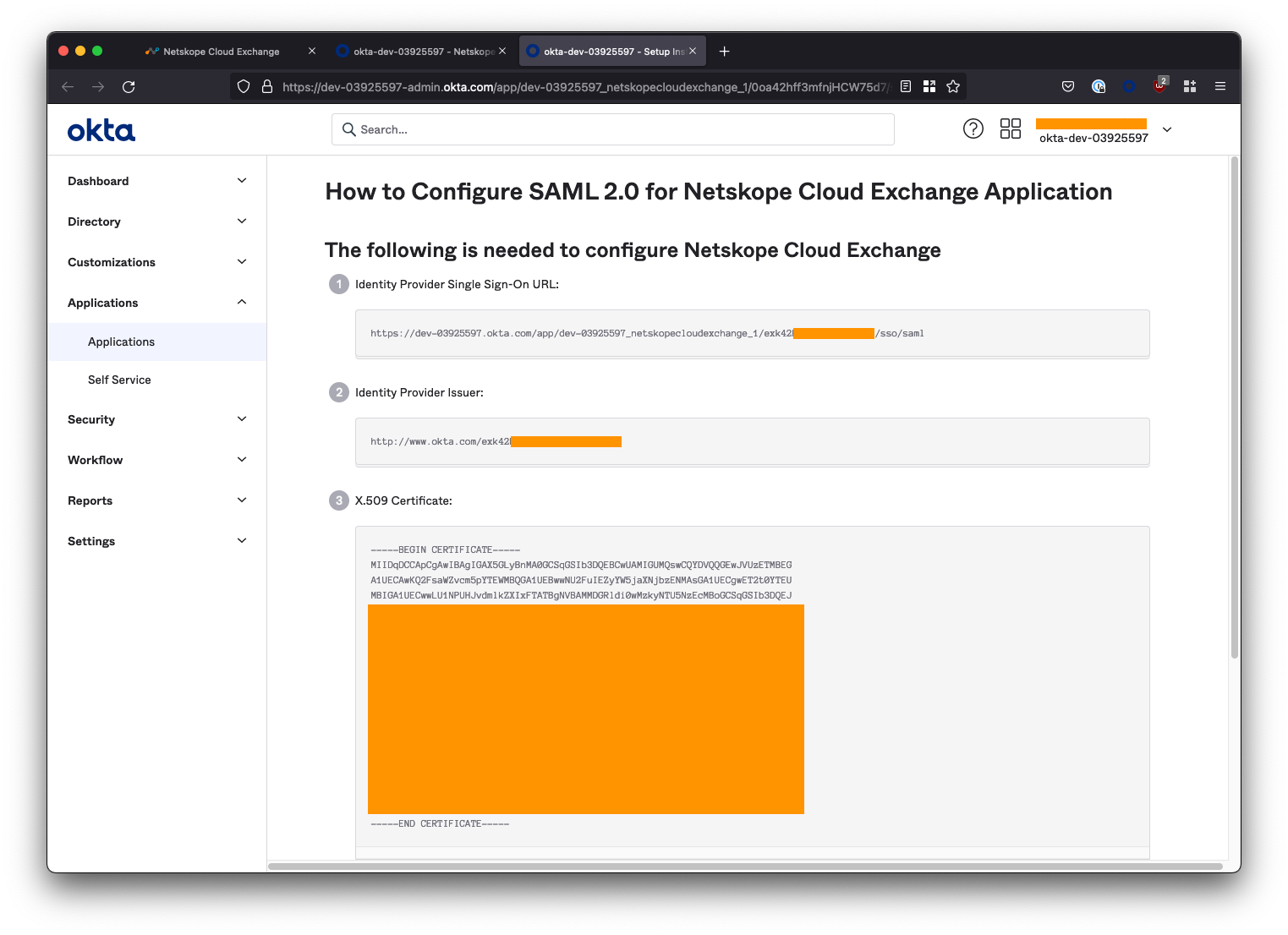
Leave this tab open for now as we still have some configuration left to do on the Okta side.
Create the roles attribute in Okta
Users can be assigned Read/Write or just Read access to the CE UI based on one of two roles assigned to them: Admin (read/write access) and Read Only. We need to create the roles attribute in Okta so that it can be used and assigned to the groups of IT admins who will use the CE application.
Navigate to Directory > Profile Editor from the left-side menu, and select the Netskope Cloud Exchange User profile.
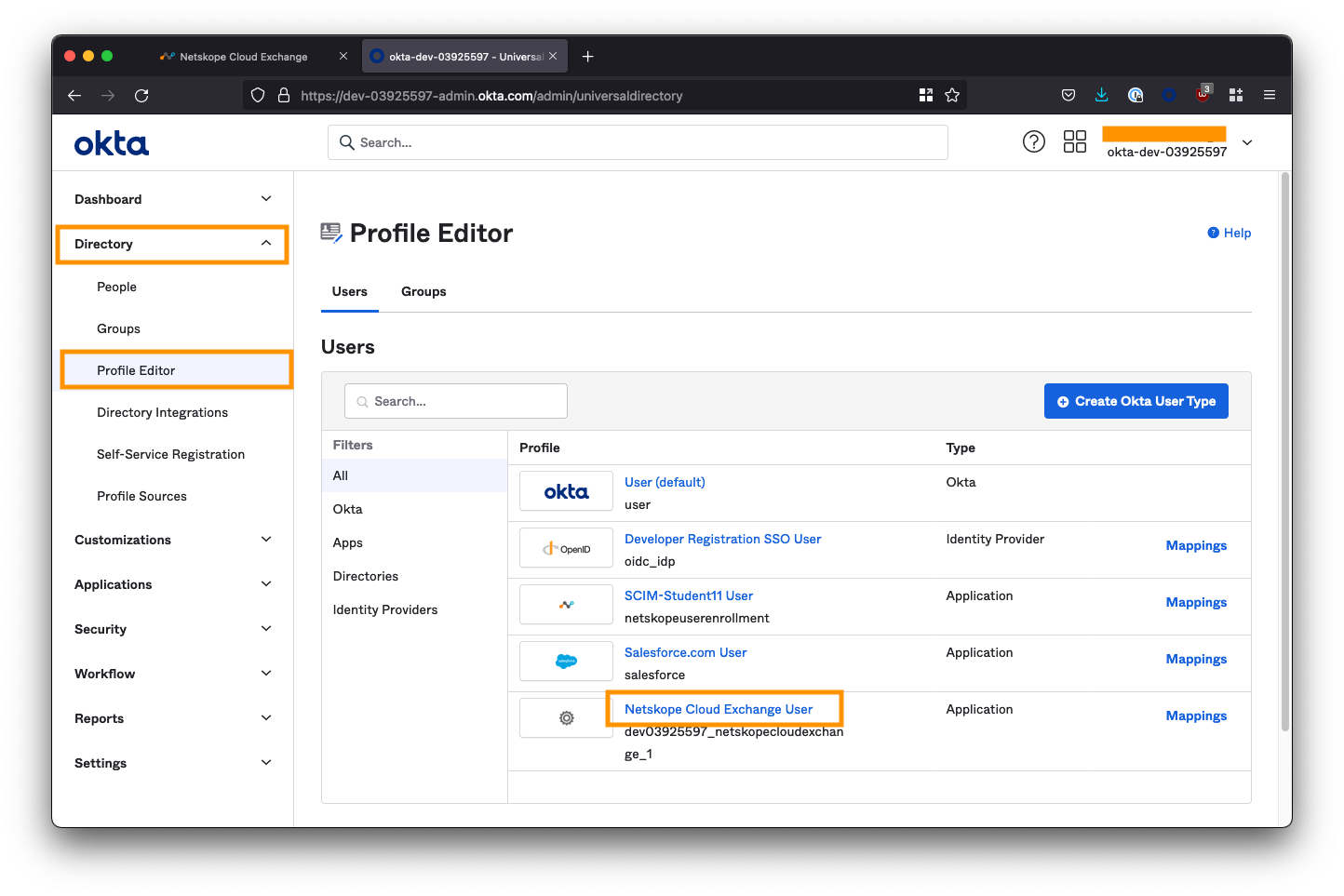
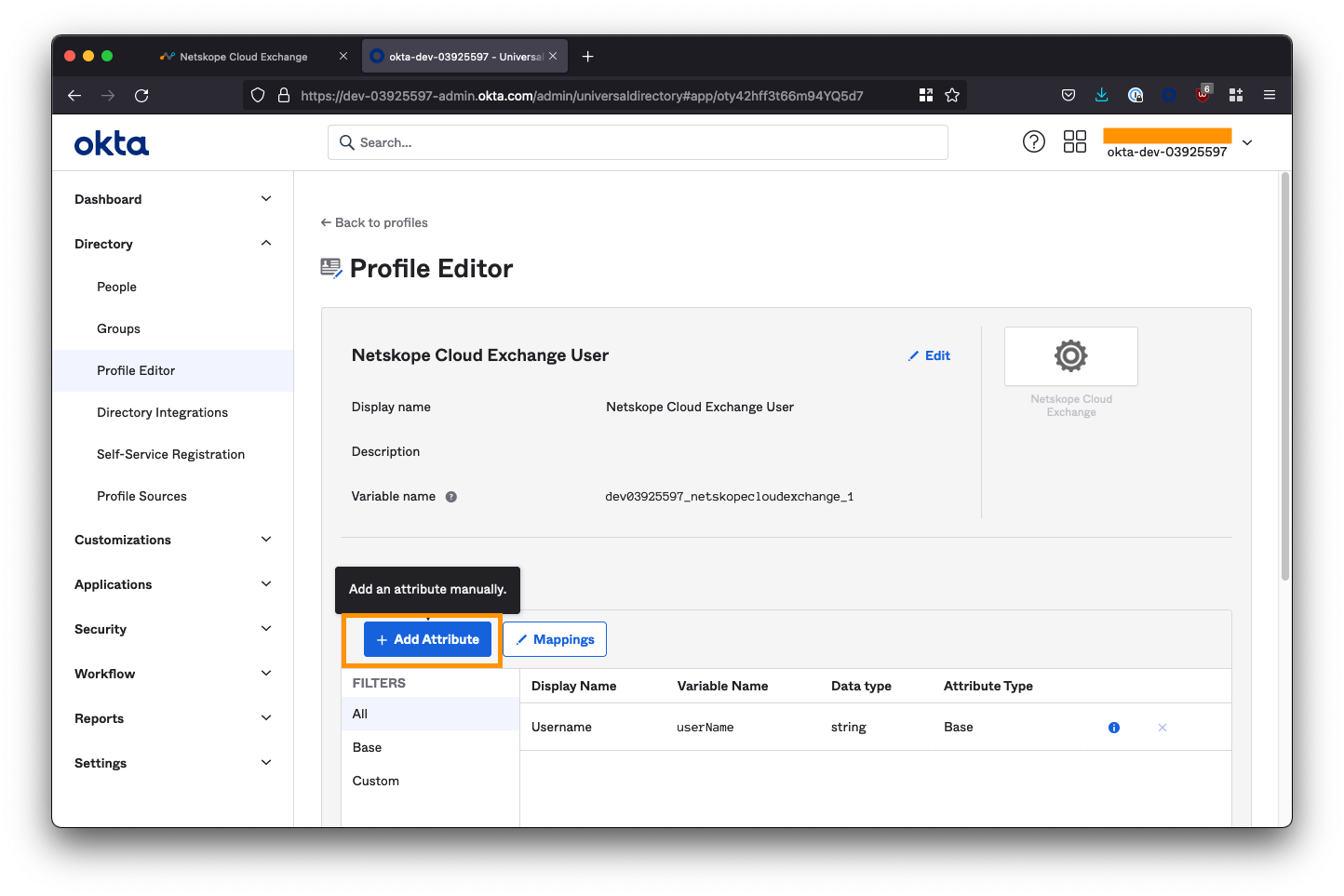
Here you’ll see the username attribute we added when we completed the SAML configuration, but the roles attribute is nowhere to be found! We need to create it manually.
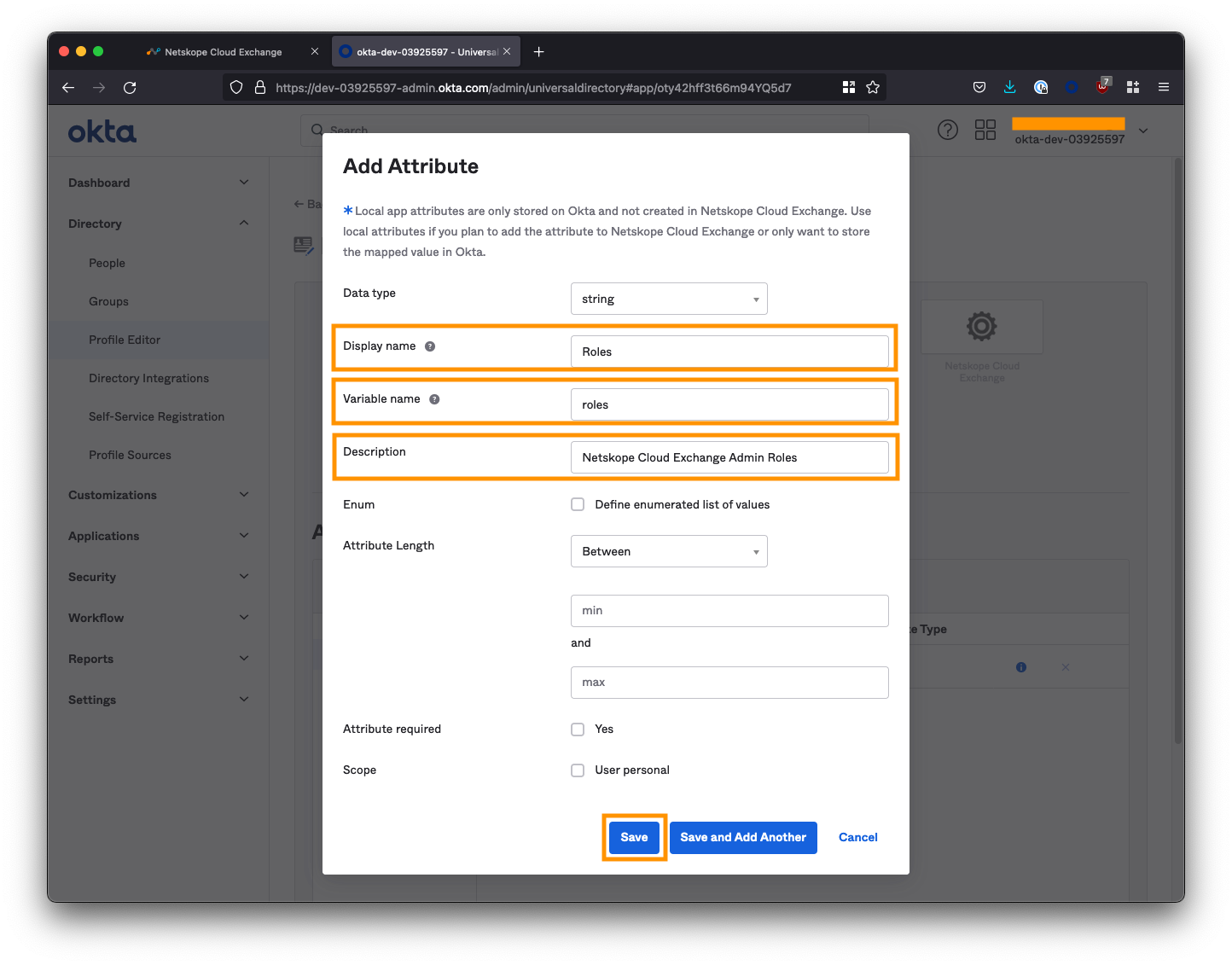
Click the Add Attribute button.
- For Display name, enter
Roles - For Variable name, enter
roles<– Case sensitive! - For Description, enter
Netskope Cloud Exchange Admin Roles
Click Save at the bottom when you’re done.
Configure User Groups for CE Access
Next, we need to create two groups: One for the users that will have read/write access to CE, and another for users that will have read-only access.
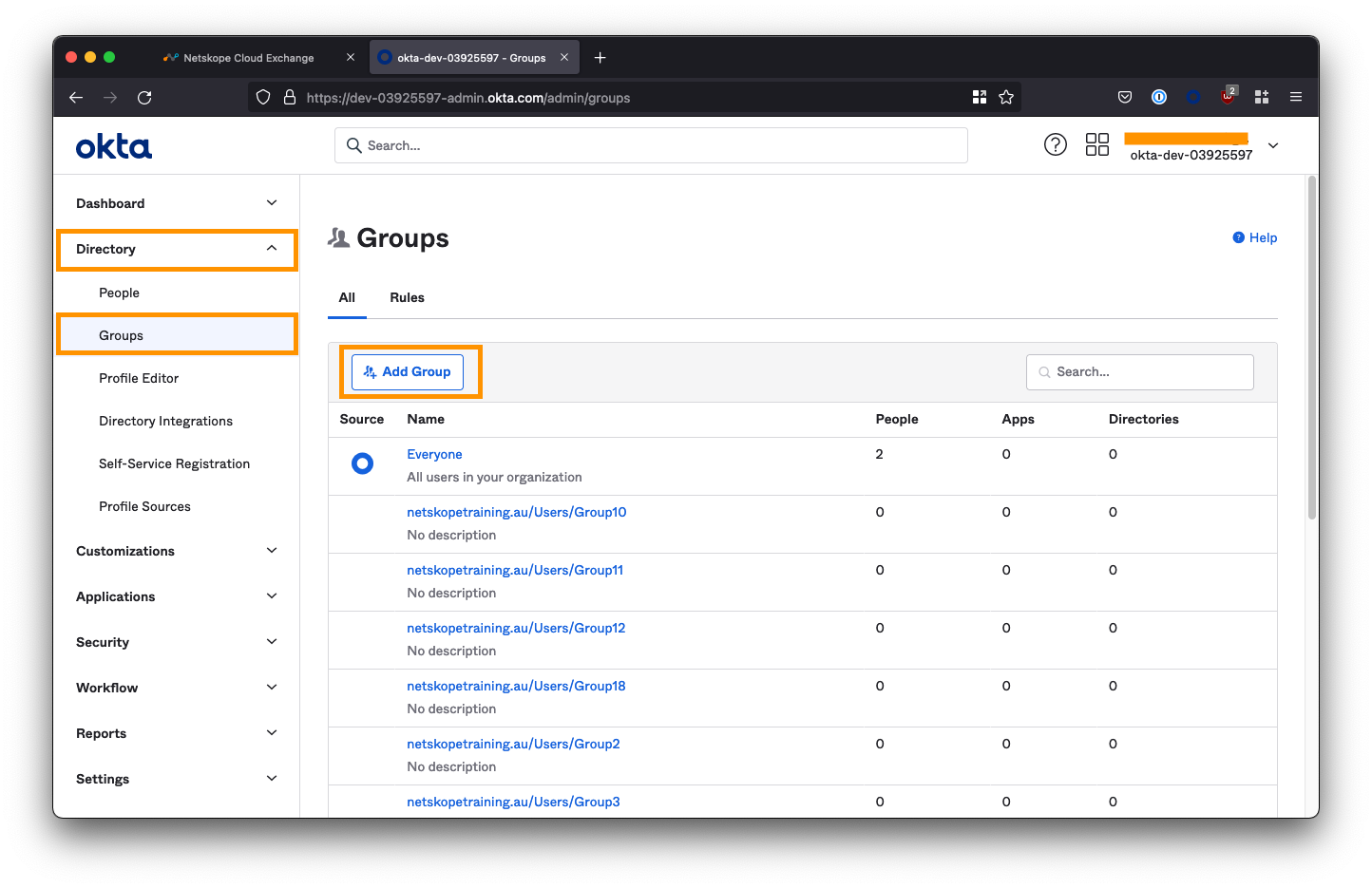
Navigate to Directory > Groups from the left-side menu, and select the Add Group button.
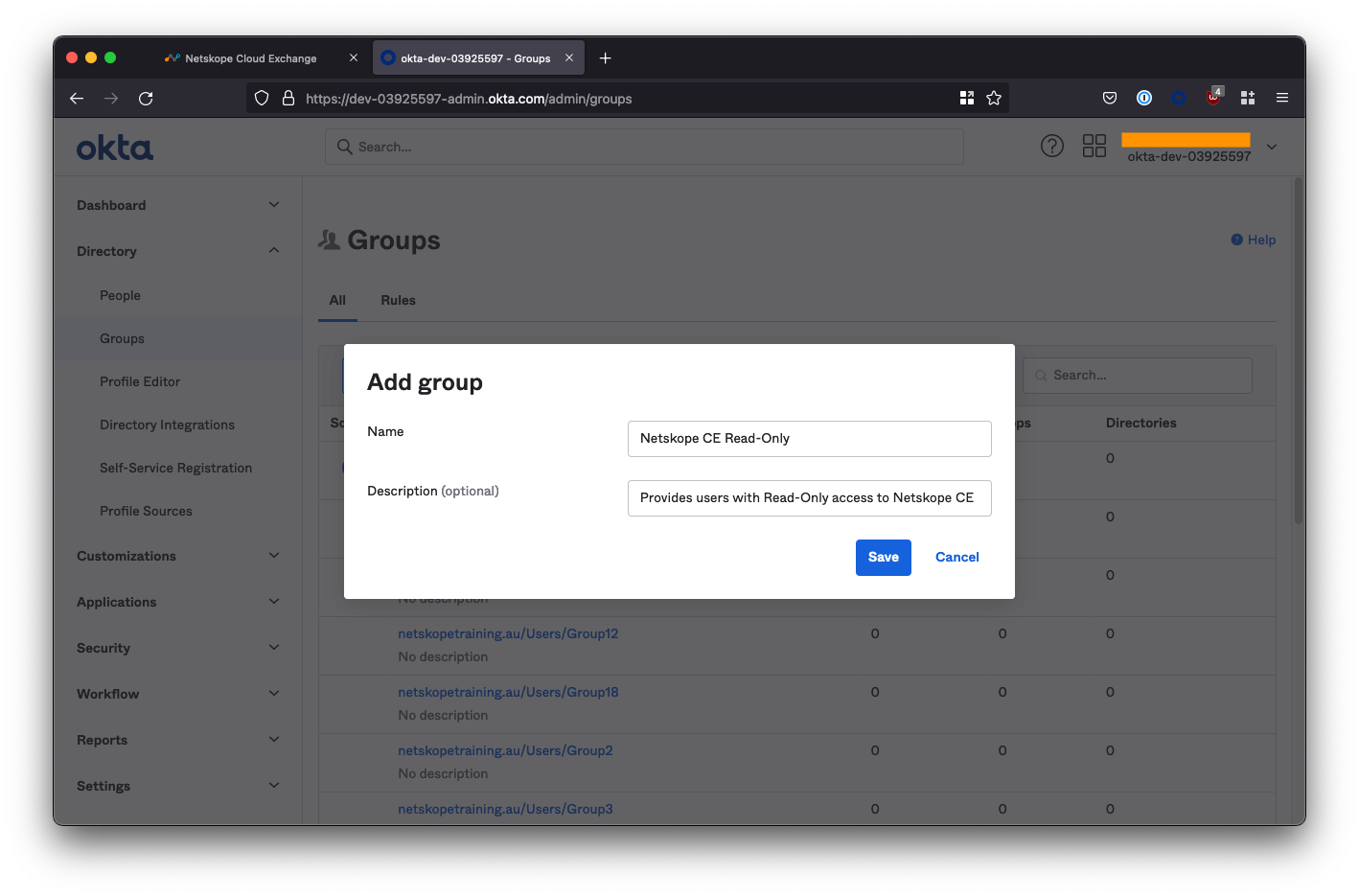
Create the Read-Only and Admin groups
Create two groups called Netskope CE Read-Only and Netskope CE Admin respectively.
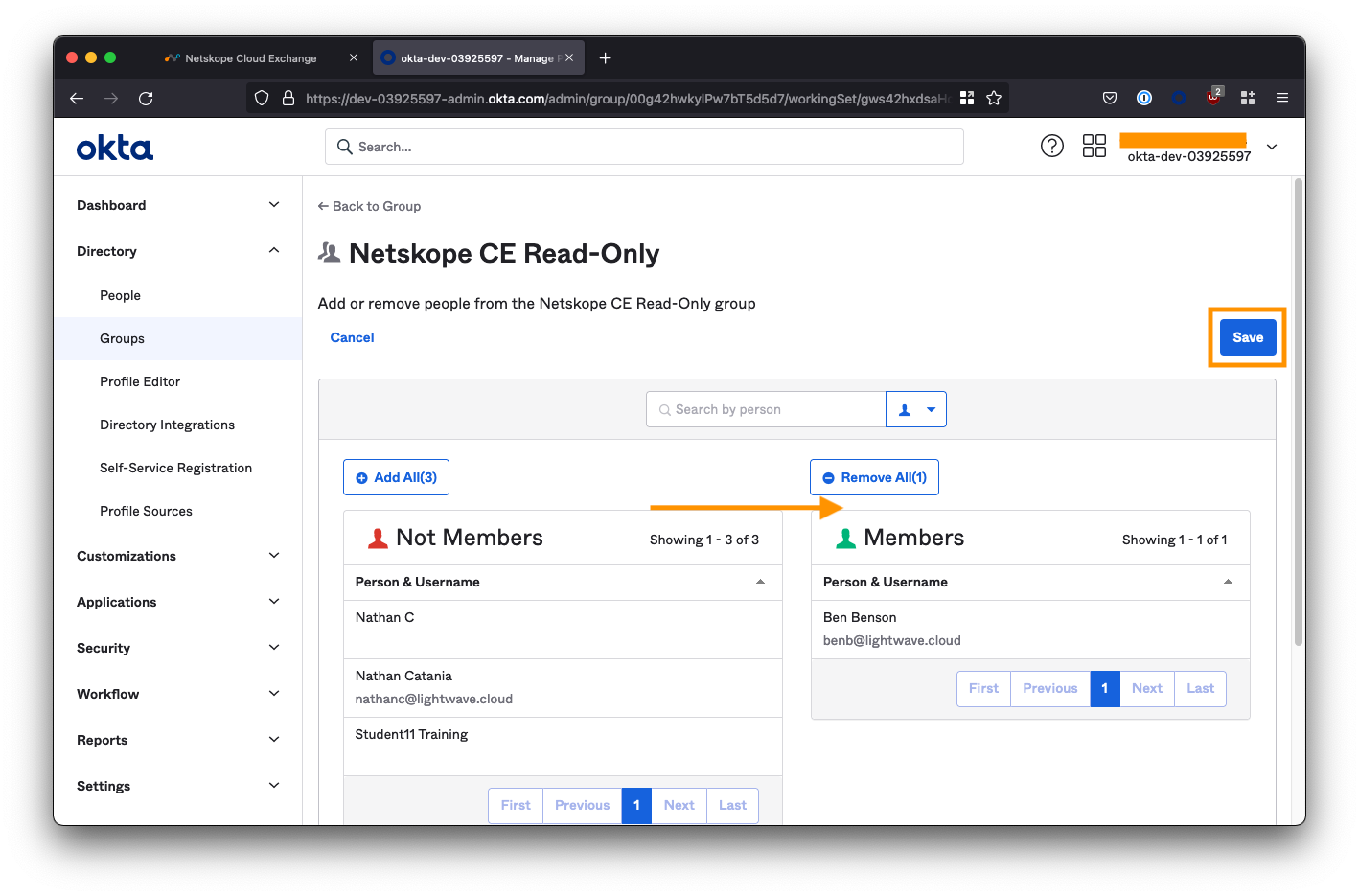
Assign people to the Read-Only role
Click the Netskope CE Read-Only group you created from the group list to edit the group.
Under the People tab, click Assign People and assign the users who will have read-only access to the CE platform. Don’t forget to click Save.
Next, select the Applications tab and click Assign applications.
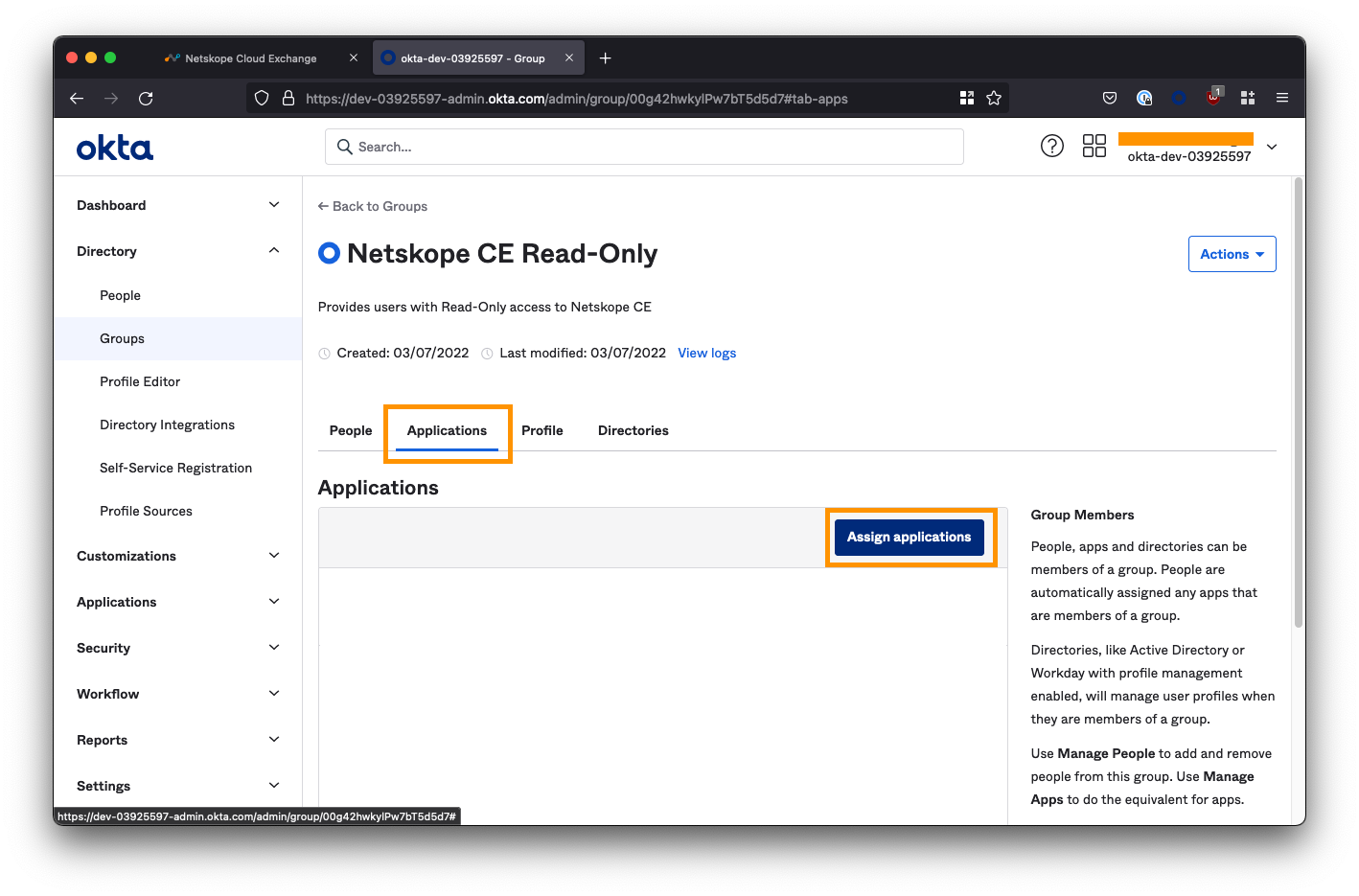
Assign the Netskope Cloud Exchange application.
You will then be prompted to specify a role. Enter netskope-ce-read
WARNING: You must enter this exactly, or SSO will fail! It is case sensitive.
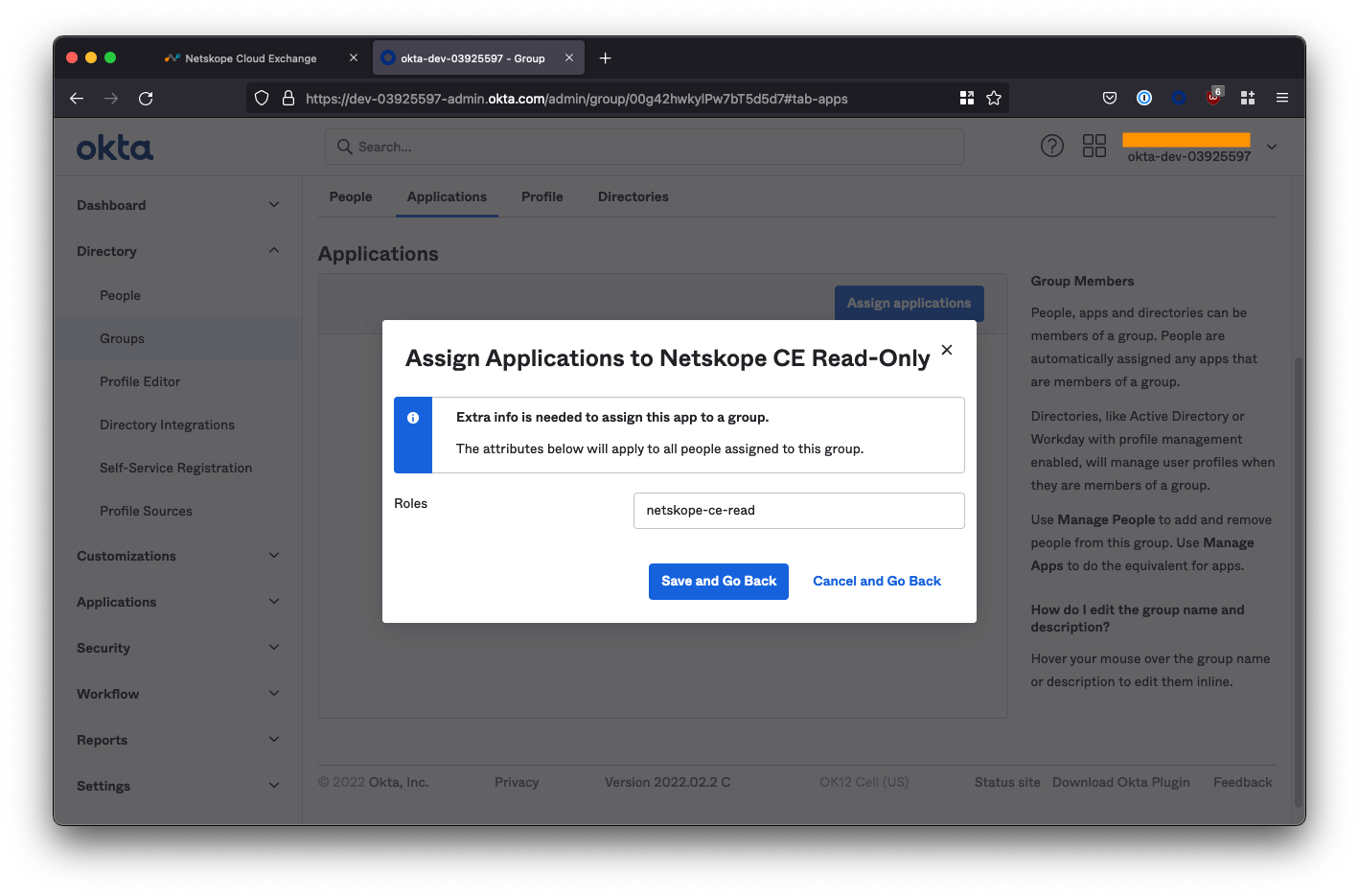
Select Save and Go Back to complete the configuration of the read-only group.
Assign people to the Admin role
Click the Netskope CE Admin group you created from the group list to edit the group.
Repeat the steps above, except this time select the people who will have read/write access to the CE platform. Don’t forget to click Save.
When prompted to specify a role, enter netskope-ce-write;netskope-ce-read
WARNING: You must enter this exactly, or SSO will fail! It is case sensitive.
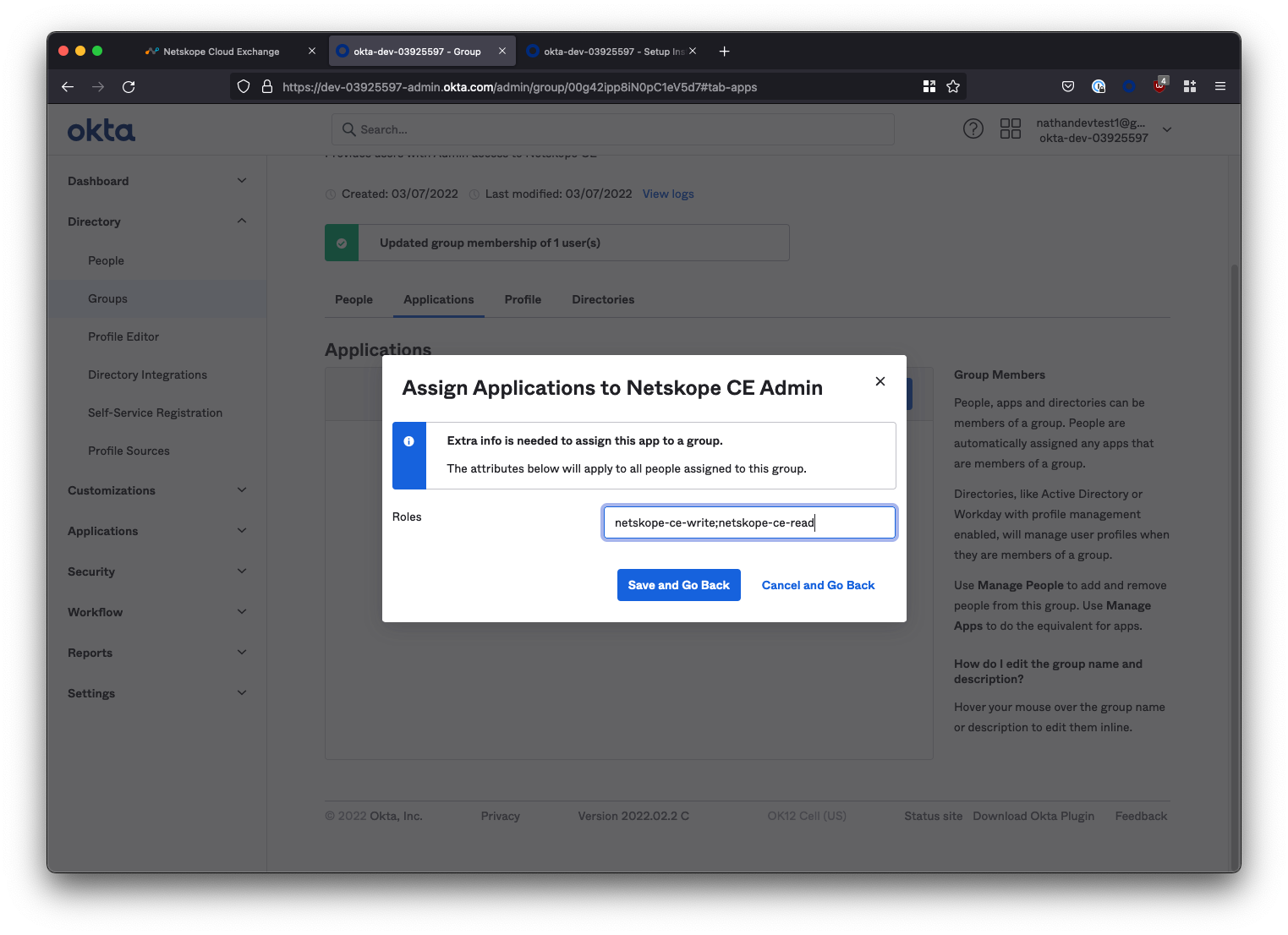
Select Save and Go Back to complete the configuration of the Admin group.
Finish the SSO Configuration in Cloud Exchange
Return to the SSO Configuration section of the Cloud Exchange UI (Settings > Users > SSO Configuration). Here we will use the details within the Setup Instructions that we opened (in a separate tab) earlier.
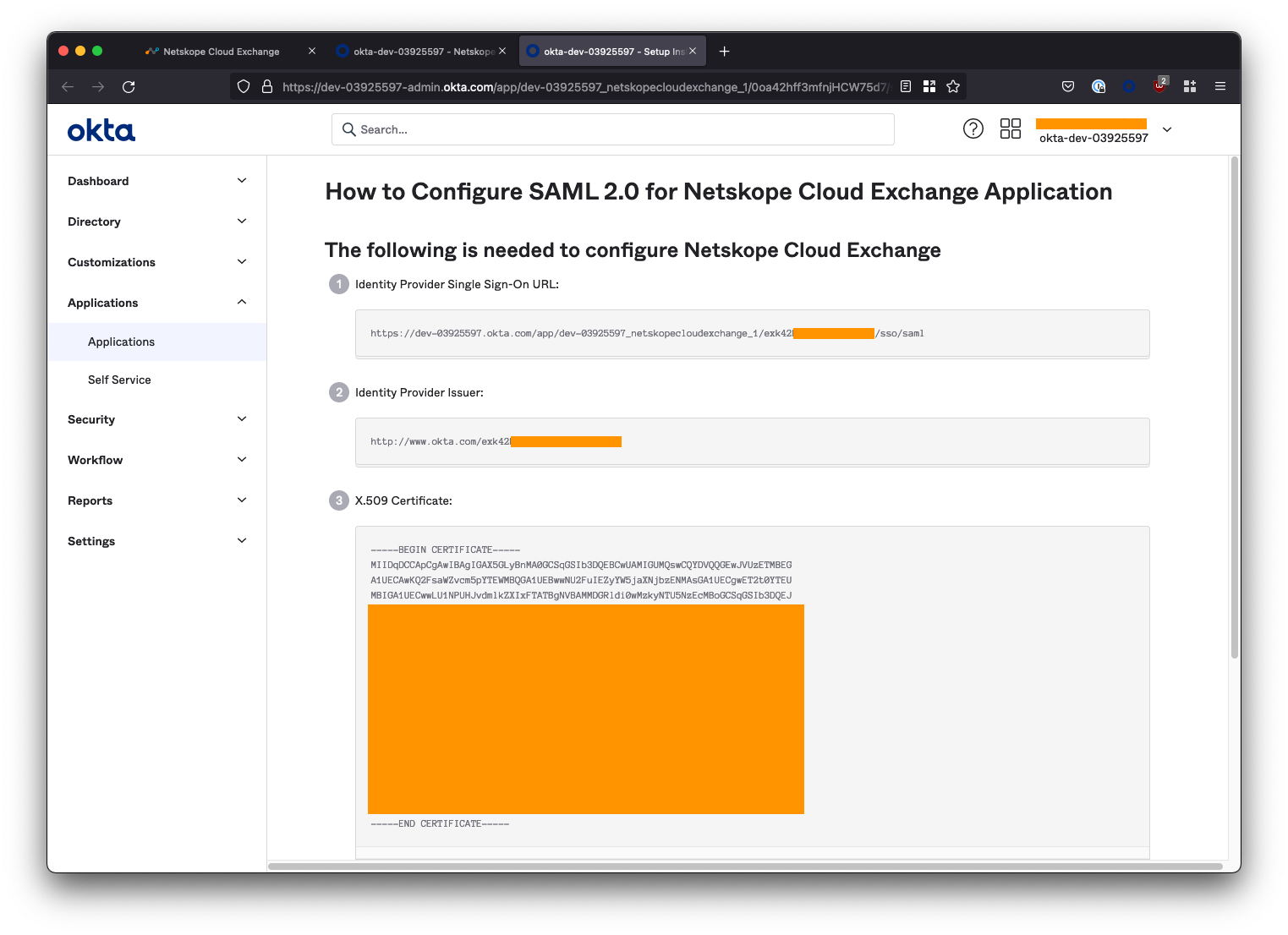
For the below fields in the Cloud Exchange SSO configuration, paste the corresponding information from the Okta Setup Instructions. See the table below for mapping:
| Cloud Exchange Field | Okta Setup Instructions Field |
|---|---|
| Identity Provider Issuer URL | Identity Provider Issuer |
| Identity provider SSO URL | Identity Provider Single Sign-On URL |
| Identity provider SLO URL | Identity Provider Single Sign-On URL |
| Public x509 Certificate | X.509 Certificate |
The SLO URL field is not needed, but cannot be blank. Copy the same URL used for the Identity provider SSO URL for this field.
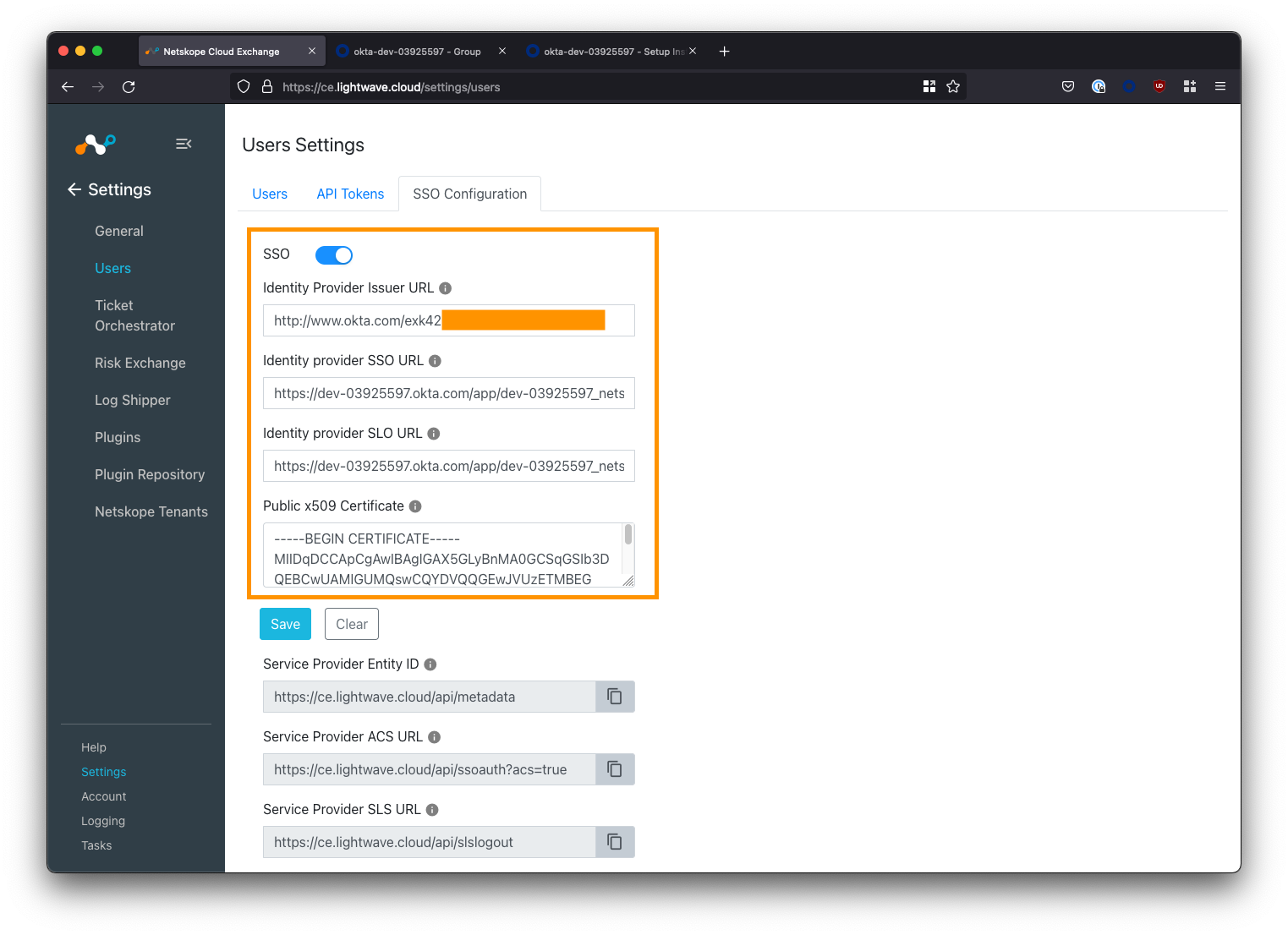
Save your SSO Configuration when done.
Testing the SSO Configuration
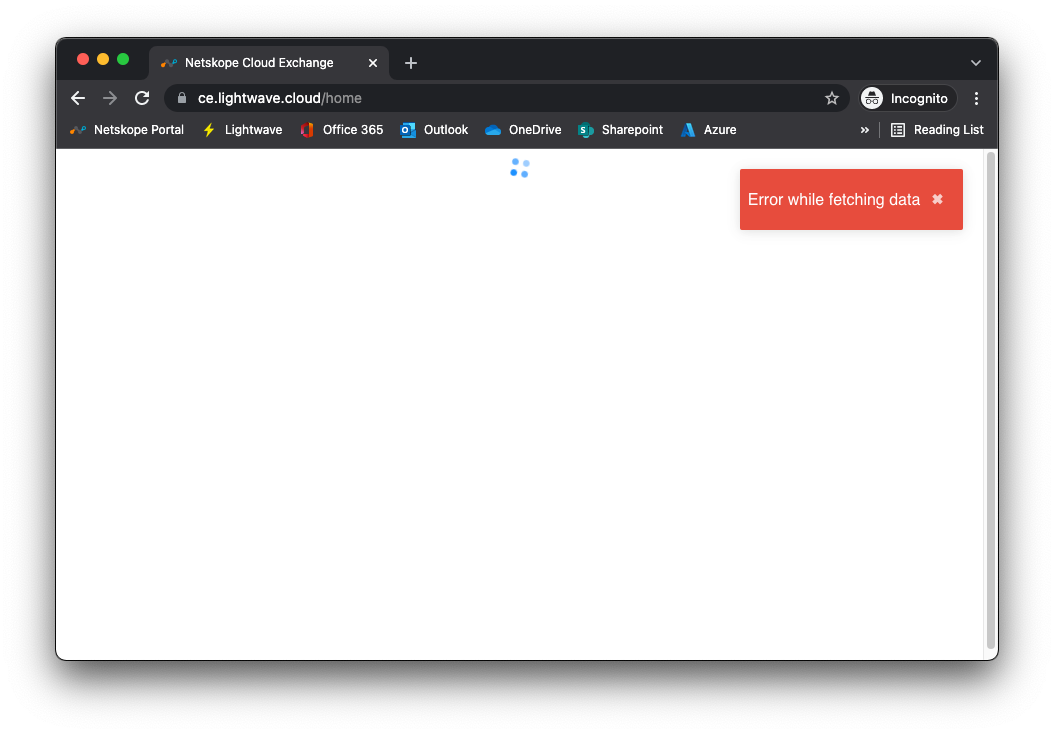
Open a new Incognito window (to avoid any potential issues with caching) and point your browser to the URL of your Cloud Exchange deployment.
If you enabled the “SSO” checkbox as instructed at the beginning of this guide, you will two options when reaching Cloud Exchange:
- Login with SSO
- Login with Username/Password
Option #2 is used for local login (ie: the default admin user, or any user manually added to the user list in CE).
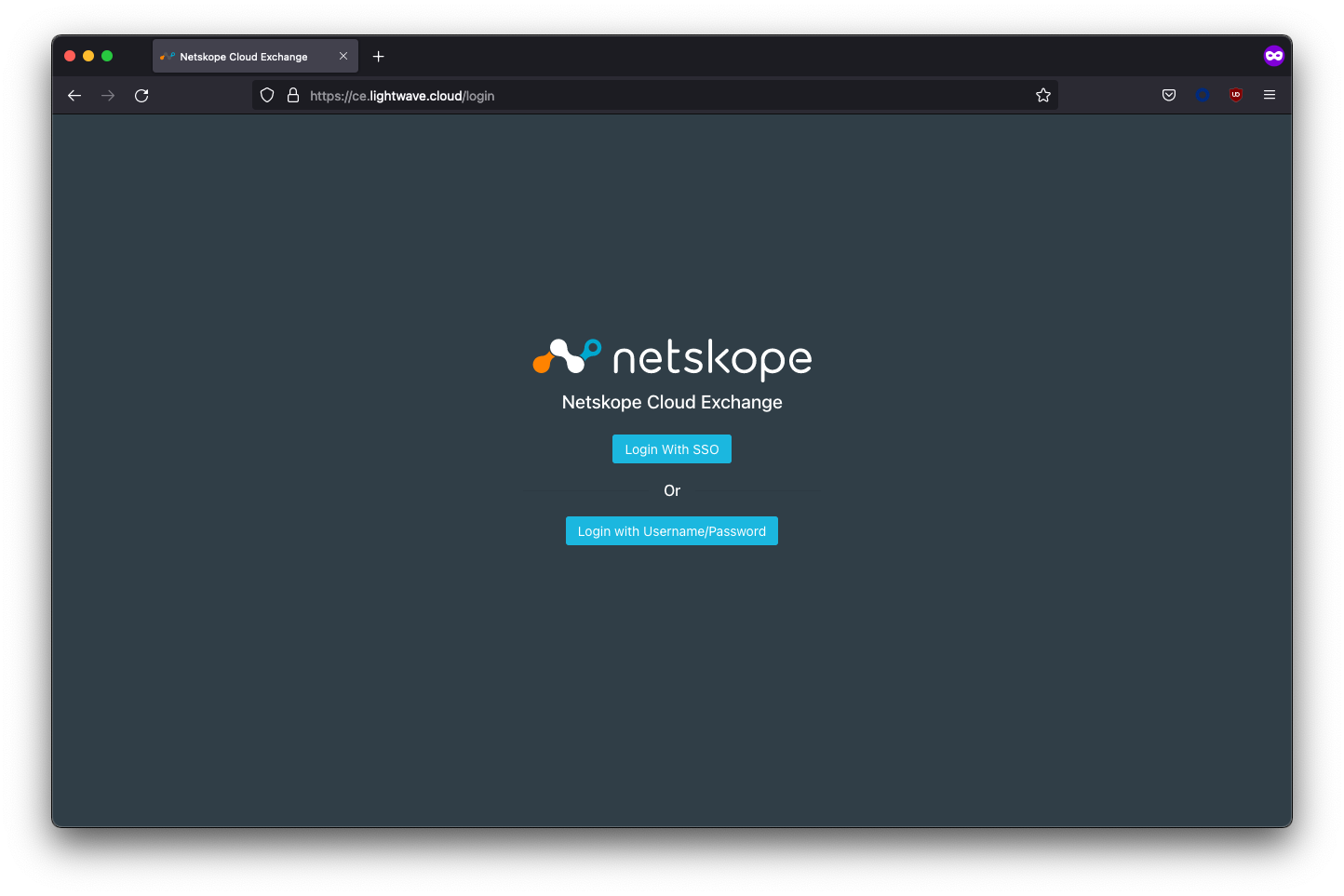
Select Login with SSO. You should be redirected to Okta to sign in.
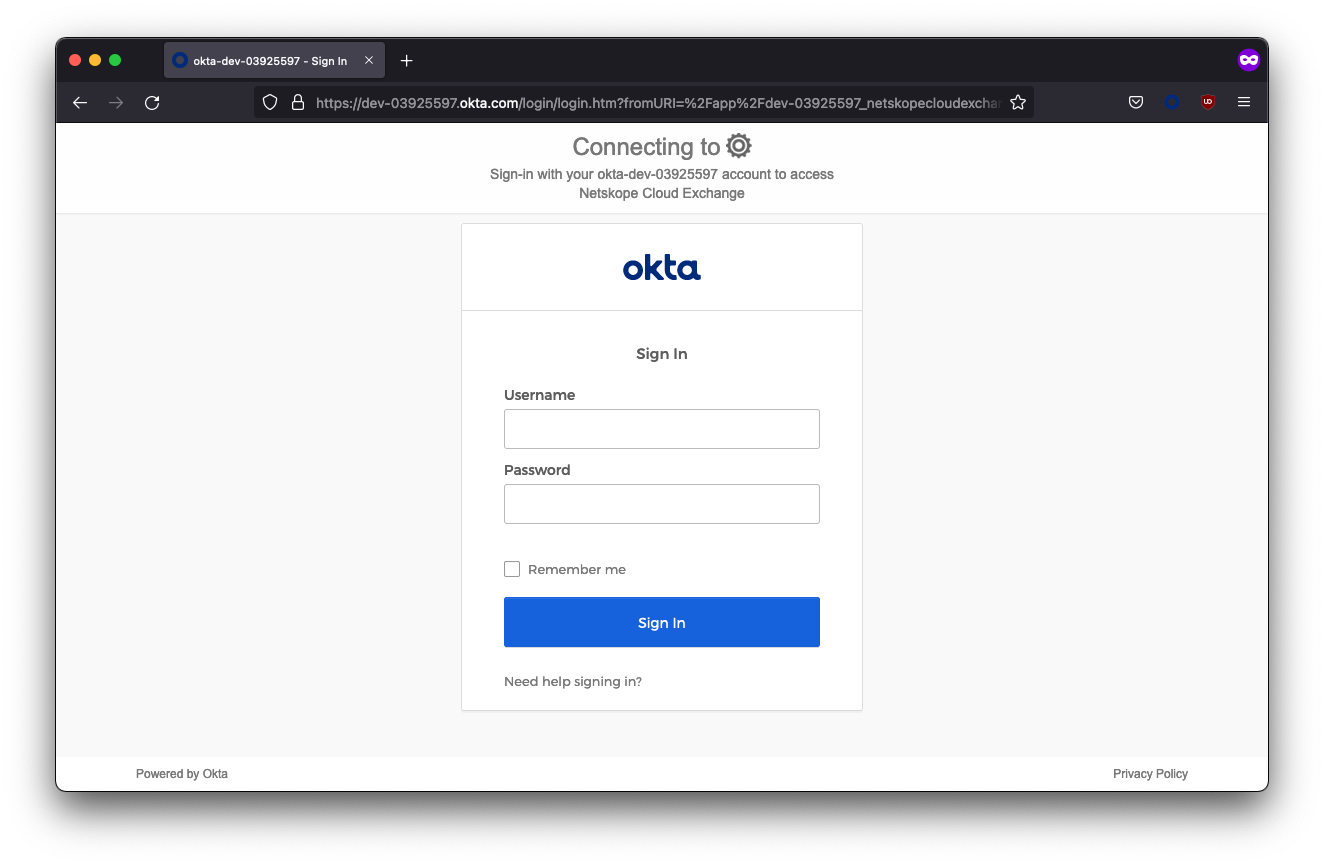
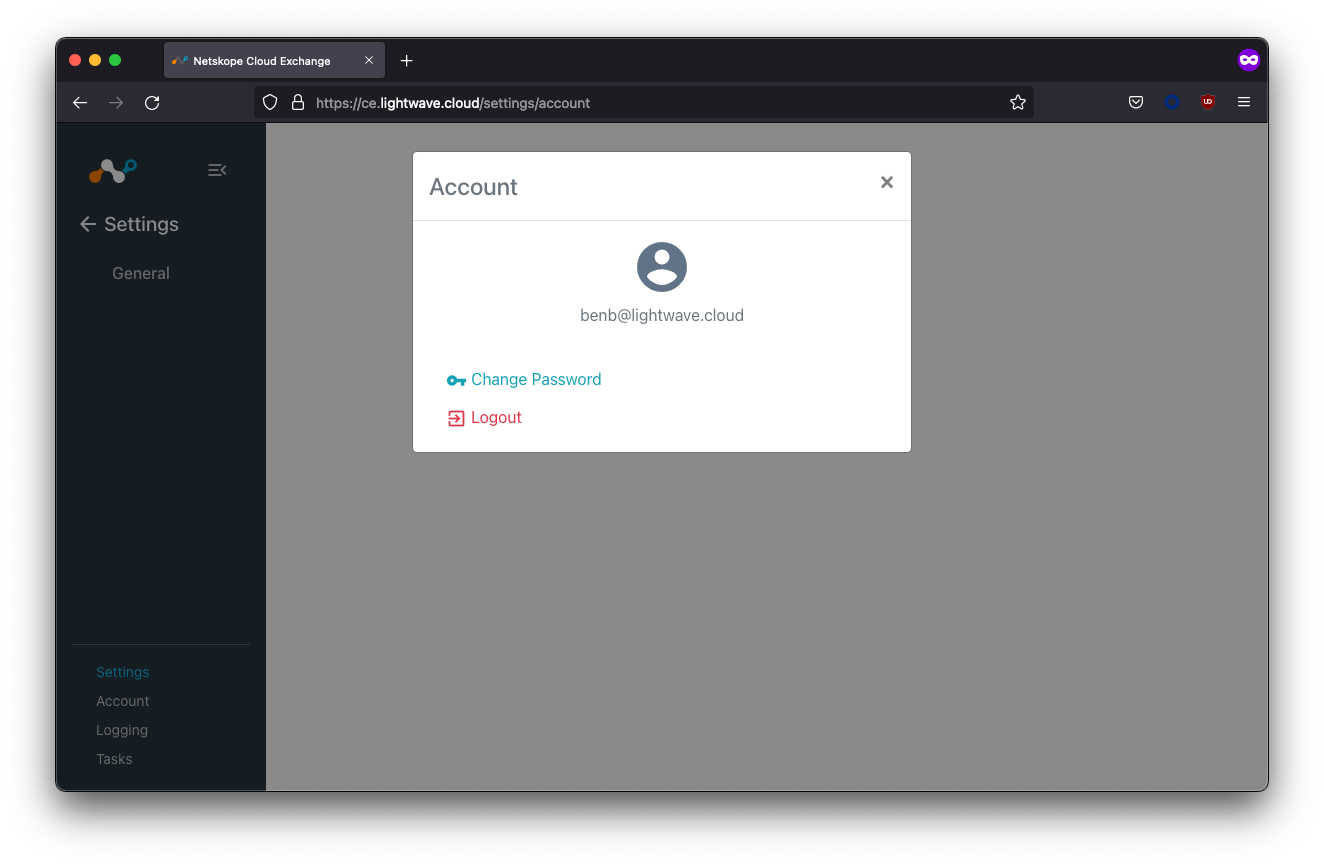
Upon entering your user credentials, you should be authenticated and redirected to the Cloud Exchange interface.
In the example below, the Ben user was assigned to the Netskope CE Read-Only group, so almost all of the Settings menu is hidden.
Troubleshooting
If you are having issues signing in, first, look at which platform is giving you an error: Okta, or Cloud Exchange?
If the error you are presented with is from Okta, then the issue is likely with your config on the Okta side. Double-check your URLs and/or whether the user you are attempting to sign in as is assigned to either the Netskope CE Read-Only or Netskope CE Admin groups.
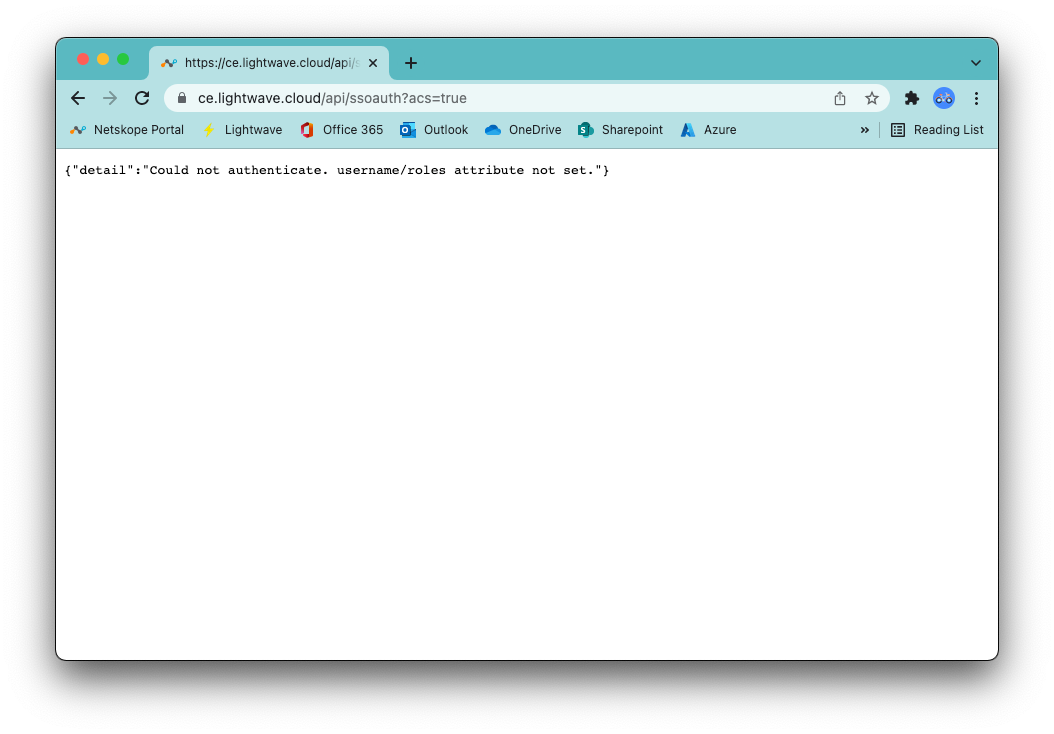
If you are getting an error from Cloud Exchange, then you have likely stuffed up the URLs entered into either CE or Azure AD, not added the custom username and roles attributes, or not typed the name of the role correctly (ie: netskope-ce-read and netskope-ce-write;netskope-ce-read).
If you get the error {"detail":"Method Not Allowed"}, check that the URLs copied into both Okta and Cloud Exchange are correct and in the right place.
If you get the error {"detail":"Could not authenticate. username/roles attribute not set."}, then check that you have added the username and roles claims in the SAML config.
If you pass SSO fine but receive a red Error while fetching data message in CE, then there is a problem with the role you have assigned to the user. Ensure you entered netskope-ce-write;netskope-ce-read as the attribute for the Admin group (Netskope CE Admin) and netskope-ce-read as the attribute for the Read-Only role (Netskope CE Read-Only).
Additionally, check that you have assigned one of these groups to your impacted user: You may also get this error if anything else has been entered into the role field apart from the above two accepted strings.