Hello,
I am implementing a new proposal for Real Time Policies for Netskope, to follow best practices and reduce the number of polices to the minimum possible.
Currently, I propose a structure similar to this (+ other specific policies of allow, block, dlp, threat protection etc..):
- Allow corporate App Instances
- Allow "Sanctioned" Apps
- Block not allowed Categories
- Allow allowed Categories
But there are webpages that belong to a non-permitted category, but to which access must be allowed. The problem is they are webpages and not applications, I can't apply the "Sanctioned" tag. If I create a custom app with the URL of the webpage, it also does not allow adding the "Sanctioned" tag.
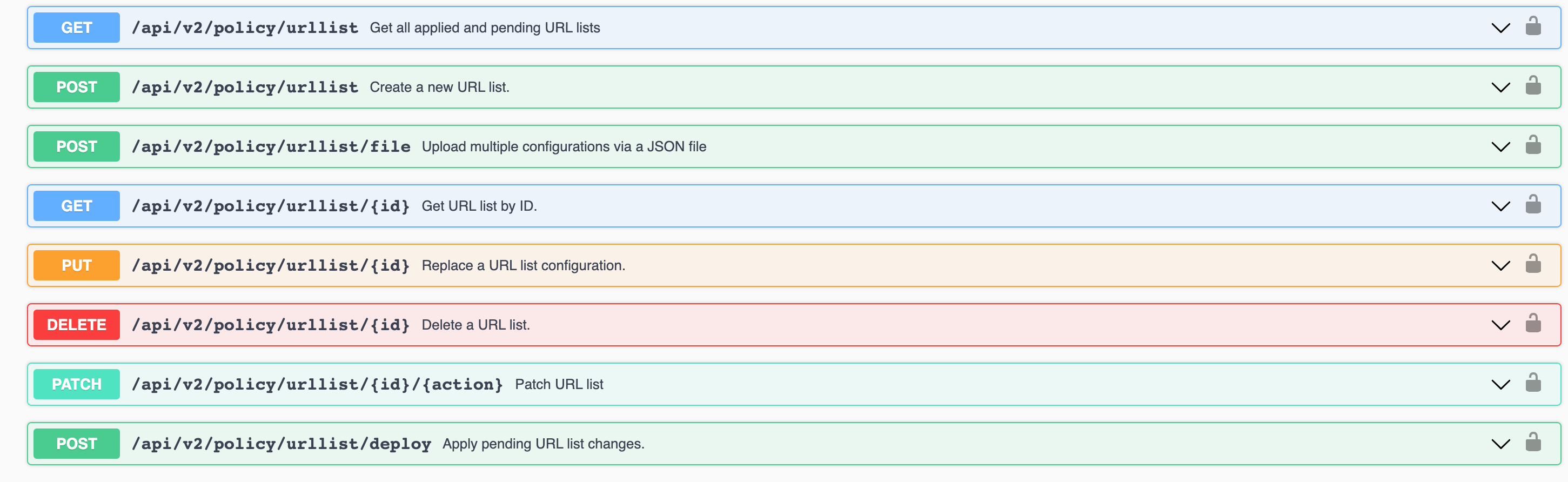
What is the best practice recommendation to resolve the situation? I can only think of creating a new policy that is allow access to a custom URL List, but it doesn't seem like a maintainable option over time, if the URL list grows too much.
Thank you so much!